TrustDump: Reliable Memory Acquisition on Smartphones
1
September 1, 2014
2
Motivation
Background
TrustDump Architecture
Implementation Details
Evaluation
Summary
3
Motivation
Background
TrustDump Architecture
Implementation Details
Evaluation
Summary
4
In-the-box approach (Thing et al., 2010; Sylve et al., 2011)
Virtual Machine Introspection (VMI) (Yan et al., 2012)
Vulnerable to armored malware using anti-forensics
Trusted Computing Base (TCB) is large
Hardware-based solution: ( Android Debug Bridge (ADB),
JTAG, Chip-off)
ADB and JTAG: need the support of the forensic target
Chip-off: physical damage and usually irreversible
5
Reliable
Against malicious mobile OS
Withstand mobile OS crash
Small TCB
Non-invasive
ARM
TrustZone
6
TrustZone
TZIC (TrustZone Interrupt
Controller)
A system-wide approach
Two isolated execution
Change
domains: secure domain and mode
normal domain
Secure interrupt--FIQ
Non-secure interrupt--IRQ
GPIO (General Purpose I/O)
SCR.NS=0
SCR.NS=1
Monitor
SMC or
other
methods
SMC
Supervisor
FIQ
……
System
Set
NS=1
Supervisor
FIQ
……
System
Non-secure
Privileged
Mode
Secure
Privileged
Mode other
than Monitor
Mode
User
User
Non-secure
State
Secure
State
Change
mode
7
Trusted Application (TA) deployed in TrustZone in the
payments at point of sale (POS) (Marforio et al., NDSS’14)
Trusted Language Runtime in TrustZone (Santos et al.,
ASPLOS’14)
Isolate Guest OS and Hypervisor with TrustZone (Kalkowski et
al., FOSDEM ’14)
8
Normal Domain
Secure Domain
Remote Monitor
TrustDumper
Reliable
Switching
Rich OS
Data
Acquisition
Monitor
Analysis
Exporting
9
TrustDump Deployment
Port Rich OS to the normal domain
Install the TrustDumper in the secure domain
Reliable Switching
Normal Domain
Secure Domain
Non-maskable interrupt (NMI)
Remote Monitor
TrustDumper
Reliable
Switching
Data Acquisition and Transmission
Online and offline memory forensics
Rich OS
Data
Acquisition
Monitor
Analysis
Exporting
10
Freescale i.MX53 Quick Start Board
A Cortex-A8 1GHz Processor
1GB DDR3 RAM
4GB MicroSD card
Android 2.3.4 in normal domain
Thinkpad-T430
11
Android Porting
Access resource of secure domain in normal domain: secure I/O
interfaces
Based on the Board Support Package published by Adeneo Embedded
Intended to run in the secure domain
void secure_write(unsigned int data, unsigned int pa);
unsigned int secure_read(unsigned int pa);
Self-contained TrustDumper in the secure domain
12
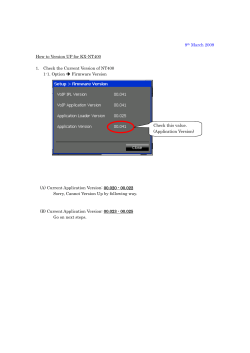
4
3
Interrupt
Engine
Interrupt
Request
AXI and AHB Buses
TZIC
FIQ
IRQ
2
FIQ
IRQ
1
Interrupt
Request
ARM Secure Configuration
Processor
Register
(SCR)
Current Program
Status Register
(CPSR)
Peripheral
Interrupt
Control Unit
13
Configure User-defined button 1 as NMI
I.
II.
III.
IV.
Enable FIQ exception: CPSR.F=0
Ensure CPSR.F cannot be modified by the normal domain:
SCR.FW=0
Enforce the ARM processor to branch to the monitor mode on an
FIQ exception: SCR.FIQ=1
Configure GPIO-2 as secure peripheral
14
Button 1 is for NMI in secure domain and Button 2 is used as
the Home Key in normal domain
User-defined Button 1 and 2 share the same access policy
Disable the non-secure access to Button 1
The non-secure access to Button 2 is disabled
15
Set the peripherals sharing the same policy as secure peripheral
Release those peripherals needed in the normal domain by
adding them into the Whitelist in secure domain
The Rich OS uses the secure I/O interfaces to access the
released peripherals
16
One interrupt number for all the 32 pins of GPIO-2
Button 2 will trigger the same NMI, instead of serving as the
Home Key as designed in the Rich OS
Forward the interrupt requests of button 1 and button 2 to
different domains
17
Normal Domain
Secure Domain
Operation
Codes
Interrupt Number
Interrupt Number
IRQ
Exception
Handler
FIQ
Exception
Handler
Rich OS
IRQ
Button
2
NMI
For
Rich OS
Monitor
FIQ
Hardware Interrupt
TrustDumper
FIQ
Exception
Handler
Button
1
18
Data Acquisition and Transmission
Integrity Checking and Rootkit Detection
current
thread_info
struct thread_info{
unsigned long flags;
int preempt_count;
mm_segment_t addr_limit;
struct task_struct *task;
……
……}
stack pointer & (0x1FFFF)
current task
next task
struct task_struct{
……
struct list_head tasks;
……
pid_t pid;
……
struct mm_struct *mm;
……}
struct task_struct{
……
struct list_head tasks;
……
pid_t pid;
……
struct mm_struct *mm;
……}
tasks
previous task
struct task_struct{
……
struct list_head tasks;
……
pid_t pid;
……
struct mm_struct *mm;
……}
struct task_struct{
……
struct list_head tasks;
……
pid_t pid;
……
struct mm_struct *mm;
……}
19
Switching time
NMI: 1.7 us
SMC: 0.3 us
Analysis time
Memory Dumping Performance
Scale (Byte)
Bit rate (bit/s)
DMA
CPU
10
92178.12
92178.49
100
92163.38
92165.45
1K
92163.01
92163.43
10K
92163.09
92163.11
Kernel Integrity Checking:
hardware (1.56 ms), software
(578.6 ms)
Processes Traversing: 2.13 ms
20
TrustDump
Reliable memory acquisition mechanism based on TrustZone
Hardware-assisted isolation
NMI as the reliable switching
Fine-grained peripheral control and fine-grained interrupt control
21
hsun01@wm.edu
© Copyright 2025